Coyote: new banking malware that steals data has 90% of cases in Brazil

Security company Kaspersky found new banking malware that attacks mainly in Brazil. This is the Coyotea threat that uses sophisticated methods to bypass security schemes.
According to Kaspersky research, more than 60 banking institutions are potential targets of this attack. Furthermore, around 90% of attacks already recorded using this method were linked to Brazilwhich means that the malware is heavily focused on national victims.
This malicious tool aims to steal sensitive information that is filled in by the user in a browser. Specifically aimed at banking websites and apps, it searches for details such as logins, passwords and access keys of these institutions.
How Coyote works
In the first stage of the infection, after being downloaded and executed by the victim, Coyote disguises itself as a simple installer. It is mainly after older machines, with outdated operating systems or fewer security schemes.
 Coyote’s path to infection.Source: Kaspersky
Coyote’s path to infection.Source: Kaspersky
This is the main characteristic of this type of threat, known as trojan — the “Trojan horse”, based on the supposed disguise strategy used in Ancient Greece.
Instead of acting like a normal program, however, Coyote uses a program update and installation tool called Squirrel. It is more complex and less targeted by security platforms, which helps to camouflage malware.
Only after hiding behind legitimate libraries does the malware actually download the malicious files to the machine. It lies in wait like a wild animal hunting, beginning to monitor the victim’s activities until the time is right.
Using SSL channels, Coyote is able to communicate with the cybercriminals’ server using encrypted messages. It is through these methods that it sends data collected from banking websites, including even screenshots.
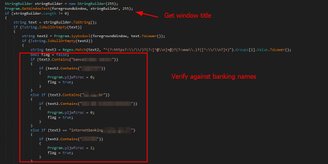
The malware code with the bank name identifier to collect data.Source: Kaspersky
For now, There are no details on who is responsible for Coyote or how many have been victims.. However, evidence indicates that it is really aimed at the Brazilian market or was even created here.
Kaspersky’s complete technical report that describes this new banking threat step by step can be read at this link (in English).